Tor
From Telecomix Crypto Munitions Bureau
Tor is
- A program that runs on your computer and makes you pretty good anonymous.
- A computer network that relays information with the purpose of making its users anonymous.
It is both of these things at once. For more info: Read this
Contents |
[edit] STOP!!!!!!!
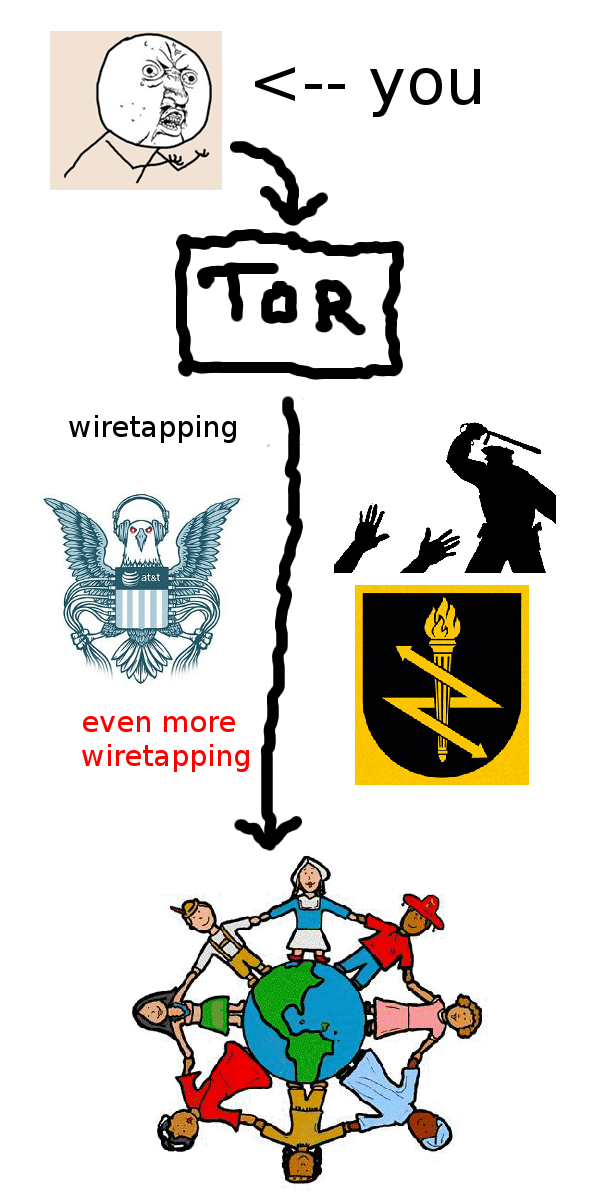
TOR only gives you an anonymous communication channel. This means that:
- You actually also need to use the anonymous communication channel TOR gives you. TOR will not automagically make you safe. Please think! Ask someone if you has not yet obtained the skills needed.
- Once your traffic leaves the TOR network, you should think of it as being wiretapped.
- Potential wiretappers do not know who they are wiretapping, unless you fuck shit up.
- Make SURE your programs use TORs SOCKS4a-proxy, otherwise DNS lookups might not go through TOR. (Check the TOR log file, it will contain notices about that.) This is really important if you suspect the military or corrupt police forces are monitoring the intertubes.
- Disable flash and javascript while using TOR!!!!!!! They leak data about you. (Only allow your browser to parse "web 1.0"-websites.)
- And finally: Do Not Type Any Personal Information About Yourself Anywhere While Using TOR, unless you REALLY KNOW what you are doing.
- Actually read these notes, make sure you understands them.
[edit] More detail of what TOR is
In brief, Onion Routing is a connection-oriented anonymizing communication
service. Users choose a source-routed path through a set of nodes, and
negotiate a "virtual circuit" through the network, in which each node
knows its predecessor and successor, but no others. Traffic flowing down
the circuit is unwrapped by a symmetric key at each node, which reveals
the downstream node.
.
Basically Tor provides a distributed network of servers ("onion
routers"). Users bounce their tcp streams (web traffic, ftp, ssh, etc)
around the routers, and recipients, observers, and even the routers
themselves have difficulty tracking the source of the stream.
.
Note that Tor does no protocol cleaning. That means there is a danger that
application protocols and associated programs can be induced to reveal
information about the initiator. Tor depends on Privoxy and similar protocol
cleaners to solve this problem.
.
Client applications can use the Tor network by connecting to the local
onion proxy. If the application itself does not come with socks support
you can use a socks client such as tsocks. Some web browsers like mozilla
and web proxies like privoxy come with socks support, so you don't need an
extra socks client if you want to use Tor with them.
[edit] Installing TOR
[edit] Any operating system
Go to the tor browser bundle-project and download the binaries. Then run them.
The Tor Browser Bundle contains everything you need to safely use TOR for browsing web pages without having to bother with asking yourself if your setup is correct and secure. It Just Works, and is perfect if you are clueless.
It will not just automatically work for everything. It just automatically makes it work with ordinary browsing web pages.
(Also, its really good for those that are not clueless too. It will make you not stand out from the crowd, while browsing. Standing out from the crowd will make it possible to fingerprint your client software. The Tor Browser Bundle will help you to avoid this.)
[edit] Windows
Go to torproject.org and click download. Then read the instructions.
[edit] UNIX
- Debian Linux: Type apt-get install tor in the terminal. Done.
- FreeBSD: Type pkg_add -r tor in the terminal. Done.
- OpenBSD: Type pkg_add -vi tor in the terminal. Done.
The following steps are optional.
- Check if it also installed torify and privoxy. Otherwise maybe think about install them too?
- torify can be used to make other programs use TOR. Just type "torify YOURPROGRAM" to make YOURPROGRAM use TOR. (torify replaces dynamically linked references to a bunch of internets-related APIs.)
- Read the torrc file (the TOR config file). It is likely placed at /etc/tor/torrc. Then make changes to it.
[edit] Android
Go to guardianproject.info/apps/orbot and get Orbot and read the instructions.
Orbot is available via Market (google) and, for your rooted smartphone, via torproject.org (latest) or the FOSS repo f-droid.org.
[edit] Hidden services?
If you have not yet read the TOR config file, read it now. Inside the config file you will find something that looks like the below, except its commented out. Replace it with whatever you want to be hosting anonymously. It is possible to have multiple hidden services running at once. Below are three different services, one SSH- and telnet-server and two webservers.
- HiddenServiceDir --- The place where you wish to store the cipherkey & hostname used for the service. Inside this directory, two files will be created once you has started TOR: hostname and private_key. The contents of the hostname file is the TOR address you can use to access your hidden service. Publish it anonymously if you want others to be able to reach your service. The contents of private_key should never be published.
- HiddenServicePort --- Your hidden service is listening on some port numbers. The first argument is the port number that your hidden service listens at, the 2nd argument is the host:port that all connections should be forwarded to.
HiddenServiceDir /usr/local/etc/tor/data/hidden_ssh_and_telnet HiddenServicePort 22 127.0.0.1:22 HiddenServicePort 23 127.0.0.1:23 HiddenServiceDir /usr/local/etc/tor/data/hidden_webserver0 HiddenServicePort 80 192.16.0.54:80 HiddenServiceDir /usr/local/etc/tor/data/hidden_webserver1 HiddenServicePort 80 www.altavista.com:80
So we have an SSH and Telnet service that connects to the same machine that runs the TOR node. We also have a webserver listening in our LAN, which we forwards requests to. And we are also making prank calls to altavista.
Please beware:
- Do NOT use virtual hosts to separate your web services. You can verify that this is a bad idea by crafting your own HTTP GET messages (using for example netcat), or by just adding the TOR-sites .onion address in your /etc/hosts file. Web servers generally does not differentiate between different types of connections, and in the worst case it will be possible to trick your server to display a hidden .onion-web page over the ordinary internet (!). The web server can easily be tricked into revealing that it is serving multiple sites, if using virtual hosts. If you do not know what this means: just run a single web page, or talk with someone that knows how the HTTP 1.1 protocol works.
- Separate services by using different ports instead. It usually is a much better idea. Do Not Forget To Test This, before you go public with your services.
- The services you provide over TOR should, unless you dont care, not also be provided over the internets. Otherwise, obviously, it will be possible to know that it is you that is providing the services. It might be a good idea to keep your server from directly accessing the internet at all (use a virtual machine or forward your hidden services to servers at a separate LAN?).
[edit] Setting up a TOR relay
If you are behind a NAT and also does not know very much about computers, please talk with someone. If you do not know if you are behind a NAT, please look at the cord that connect your computer with the internet. If the other end of the cord is connected to a modem of any kind, or a router, you need to speak with your local nerd. (AND BE NICE TO YOUR NERD.)
TOR seems to be able to recognize and automatically negotiate a path through many "ordinary" routers/modems using UPnP. So you might not have to worry too much. But if you are serious and dont know what you are doing, talk with someone.
The last section in the default torrc file is about relaying TOR traffic. It should not be too difficult to read it yourself.
Something like this probably works nicely:
ORPort 9001 DirPort 9030 RelayBandwidthRate 1000 KBytes RelayBandwidthBurst 1200 KBytes # Share slightly less than your entire 10Mbit/s connection. # If you are brave and know what you are doing, use this ExitPolicy reject *:25 ExitPolicy reject *:587 ExitPolicy accept *:* # If you are not so brave and dont want the police bashing through your door, use this ExitPolicy reject *:*
Actually, people have had the police bash through their doors because of TOR exits. But seriously, consider having an exit node. You will just have to explain whats happening to them, thats all.
[edit] Using TOR as your "default gateway"
It is possible to use TOR as a transparant proxy, so that all connections from a network with computers (such as your home LAN) goes through TOR. The computers in your network will then not be able to know that they are using TOR, and everything will be slightly slower than normal. All connections that any computer does from within your network will automatically go through TOR.
To do this, you need to have a router that runs linux or some sort of BSD. It will only work for TCP connections, because TOR only relays TCP. UDP will either have to go through your normal link to the intertubes, or be dropped. Almost everything uses TCP, so this will mostly not be a problem.
Suggestions:
- Make a public unencrypted WLAN, set the name of it to something like "Free and anon intertubes" and then make everything go through TOR. (It will of course be possible for anyone that is connected to the WLAN to see what everyone else does, since the WLAN is not encrypted or anything. But maybe that is OK?)
- Keep two different networks around. One that you use for normal internets and one that has everything go through TOR. That way, you will not have to configure stuff just to use TOR. All you would have to do is to pull out the network cable and insert it to your TORified network. (Use cables and avoid WLANs if you want to feel secure. Do not trust encrypted WLANs to be safe.)
- Make fuckin sure that you dont have security breaches. Read iptables or the OpenBSD pf tutorial. (FreeBSD lags like 5 years behind OpenBSD with their implementation of PF, so you will need to find old manuals if you insist on keeping FreeBSD around.)
How to do it?
- Go to this web page and follow the instructions.
- If that link is dead, google for "TOR transparent proxy".
- You will maybe have to setup a DHCP server too.
Make sure you follow the correct instructions, there are multiple ways to configure this.
[edit] NoScript
When you are using TOR, you should block all scripts. Why?
- You can just ignore google-analytics and everything like that. Say goodbye to googles panspectrocism.
- You dont have to view all those stupid ads trying to psyop you into paying for pr0n.
- Javascript can be used to give off information about yourself. Like your user name, IP, real name, whatever.
- Flash is closed software and has sekrit cookies that are frequently used to keep track of users, even if they remove their ordinary web cookies.
Click this link and muse over the fact that the official NoScript webpage looks sooooo much like some advertising campaign on amplified steroids mixed with amphetamine. PARADOX?!
[edit] Privoxy
In order to remove further information about yourself, you can install privoxy. Privoxy is a program that you can use to setup pretty much any form of private proxies. And it can also be configured to rewrite the TCP streams, for example to remove ads, or make all users look as if they were running windows. Or whatever. Please spend some of your time reading and modifying the config file yourself.
The trick is not to just remove all data about yourself - that will just make you stand out from the crowd. Try to make yourself look like a windows user. That way you blend in among the sheeps pretty well. Goto panoptiClick to test how difficult/easy it is to profile you.
Just add the following lines to the end of the config file:
forward-socks4a / 127.0.0.1:9050 . forward .i2p localhost:4444
This will also make privoxy work with I2P. That way you dont have to fiddle back-and-forth between different proxies just to access the other network.
Then just tell your browser to use http proxy, port 8118. (In firefox: Click on the Edit-menu -> Preferences -> the "Advanced" tab -> Select "Network" tab, press "Settings". Then type in 127.0.0.1, port 8118.)
[edit] IRC and TOR
Almost all IRC clients has support for CTCP (Client To Client Protocol, used for sending files, among other things), which can be used to reveal information about the clients. In the worst case, it can be used to reveal your real IP number, simply by asking the IRC client.
You will have to either disable CTCP or use an IRC network that disables CTCP by default. ngircd is the only IRC server around that has this support (by enabling the "ScrubCTCP" option). As far as we know, only Telecomix IRC supports this at the moment.
An alternative is to use I2P instead. It has automagical support for this at the client side. The downside with I2P is that you will not be able to connect to any other IRC networks but I2Ps internal network, and Telecomix.
[edit] If TOR is blocked, use proxychains
UNIX only: Download and install proxychains. Then make your connection go through TOR, and then through some random ordinary proxy that you know about. Then it will look like you are not a TOR user. It will of course be a bit slower than with just TOR.
Stuff worth knowing:
- Public open proxies are mostly not supposed to be public and open
- They usually go offline after a while, when the admins discover their errors
- If you use public lists of open proxies, they are already blocked because of spam, or will soon be blocked. You can use nmap and scan for open port 8080 or something :d
The config file of proxychains is pretty self-explaining. Read it, then make adjustments. Optionally also read the man page.
[edit] See Also
[edit] Problems?
- Do not forget that nerds needs to be treated nicely.
- Go to the free anon online support desk.
- Do not give up just because you do not receive an answer NOWWWWWWWWWWWWWW!!!!! Please be patient.